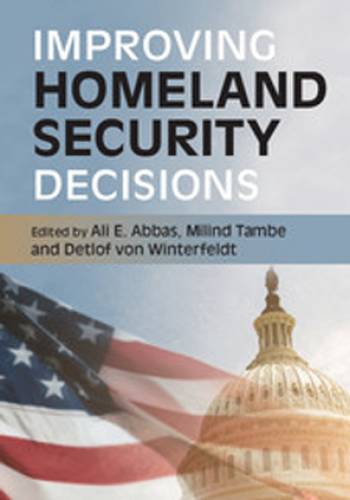
CREATE’s decision analysis researchers use rigorous models to help make sound decisions in homeland security applications related to terrorism and other catastrophic risks. Topics include:
- Representation of preferences and trade-offs using multiattribute value and utility models
- Representation of risk attitudes
- Modeling adversary beliefs and preferences
- Representation of belief using joint probability distributions and Bayesian learning
- Group decision making
- Framing decision situations
- Alternative generation
- The identification (and minimization) of cognitive biases
- Implementing a decision culture within enterprises
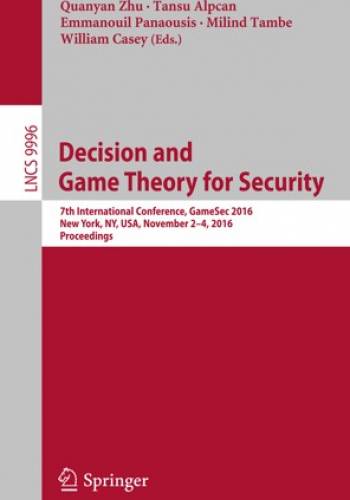
Game Theory is also applied to capture objectives and beliefs of adaptive adversaries threating critical infrastructure, including seaports, airports, wildlife/forests/fisheries, and high-crime urban areas. Limited resources must be allocated and scheduled efficiently, avoiding predictability while simultaneously accounting for adversaries’ responses to security coverage, adversary preferences, and uncertainty over such preferences and capabilities. Casting security allocation as a Stackelberg security game, our new algorithms have been used in multiple applications.